Do you know this man?
Posted by Voipfone on March 7, 2016
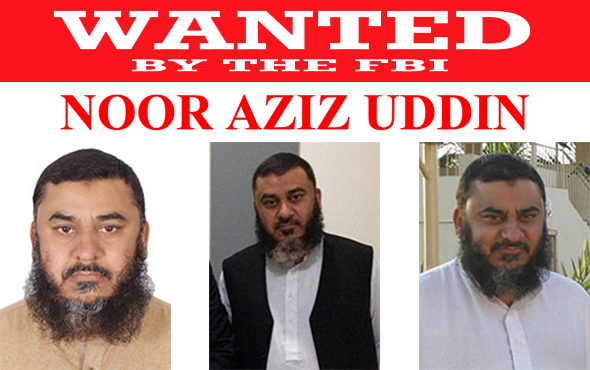 This likely-looking-lad is ‘allegedly’ responsible for $50m worth of PBX hacking fraud.
This likely-looking-lad is ‘allegedly’ responsible for $50m worth of PBX hacking fraud.
He’s been sold out by another nice chap called Muhammad Sohail Qasmani, from Bangkok. The FBI put out this:
“Thanks to the hard work of the prosecutors and agents on this case, Qasmani acknowledged his role in an international scheme that hijacked the telephone networks of U.S. companies and ran up millions in bogus charges,” U.S. Attorney Fishman said. “Today, he admitted moving over $19 million in illicit proceeds across 10 countries and ensuring the dialers and hackers who perpetuated the scheme received their cut.”
Quasmani was Aziz’s money launderer, he set-up money transfers to 650 individuals in at least 10 countries: the Philippines, India, Pakistan, Malaysia, China, the United Arab Emirates, Saudi Arabia, Indonesia, Thailand, and Italy.
Aziz is on the run. Amusingly, the FBI site tells us that despite being charged with the offence and on their most wanted list with a reward of $50,000 (a couple of hours of hacking for him) – he “is considered innocent unless and until proven guilty.”
Telephony fraud is responsible for about $46bn of loss to the industry and its customers. A large and growing share of that is VoIP fraud in various guises – a while ago a small UK business was taken for £35,560 by hackers compromising their VoIP PBX.
There are a couple of ways you can defend against your PBX being hacked and landing up with a large bill. Firstly – and best – use a hosted VoIP service like Voipfone so you don’t actually have a PBX to be hacked, but if you must have your own switch, please get it installed and maintained by a specialist with a lot of experience. ITSPA provide a free guide of how to protect yourself here:
Many people think they can DIY – don’t, it’s a huge risk. Your PBX will be scanned within minutes of attaching it to the internet and if you get it wrong or forget to update it, it becomes a bank with an open safe.



